These issues don’t break pipelines.They don’t trigger alerts. They quietly spread across your data stack.
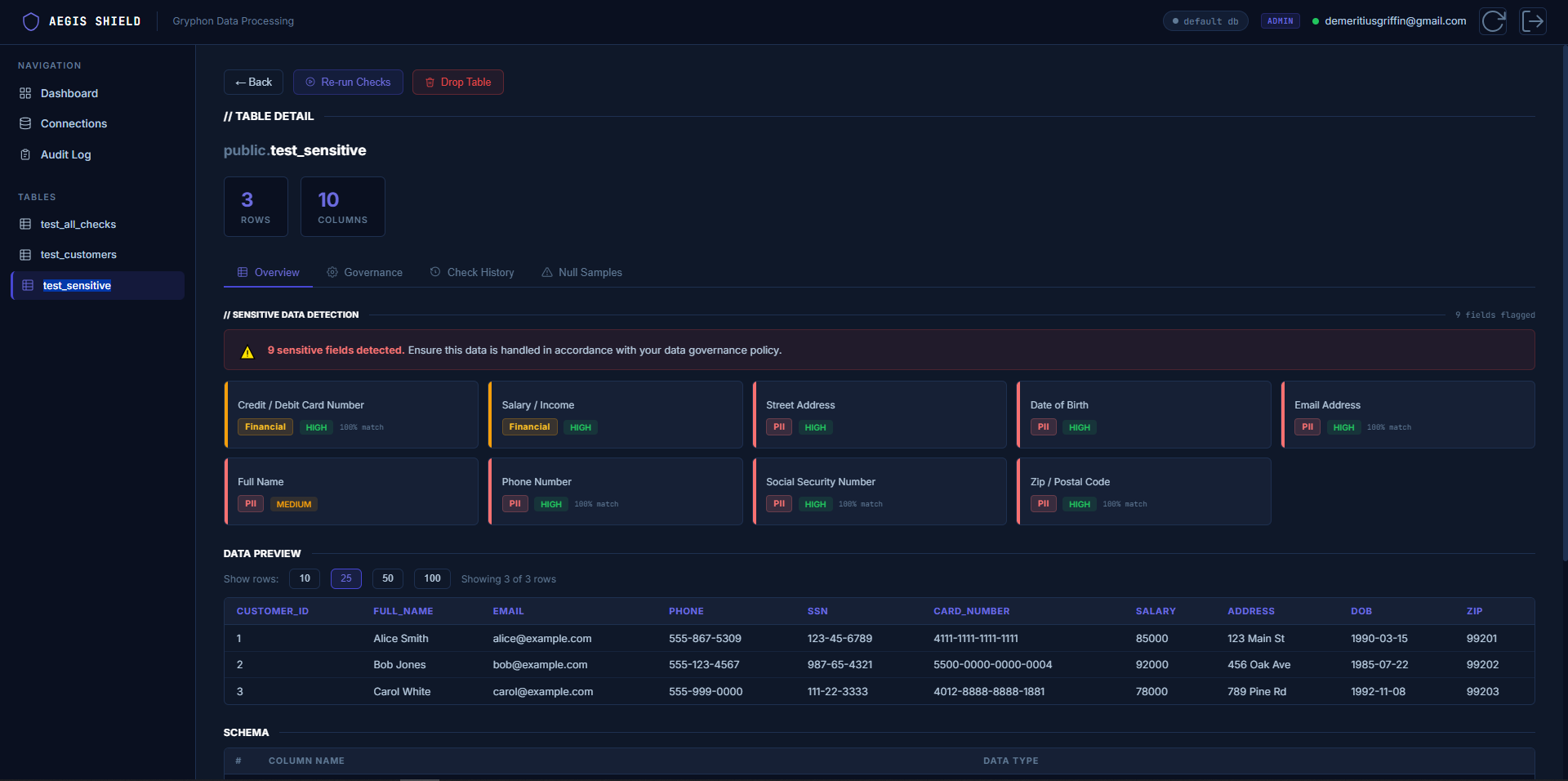
Aegis Shield automatically detects and flags hidden PII across your data stack.
It doesn’t trigger alerts.
It doesn’t break pipelines.
It only becomes visible when something goes wrong.
Six quality checks run automatically on every upload. No configuration required. Results appear in seconds, not after a CI job you'll forget to check.
No config files. No pipeline configuration. No dedicated data engineer needed.
Whether you're preparing for a compliance audit, onboarding vendor data, or building data discipline into your team — Aegis Shield fits into your workflow.
Early access customers shape the roadmap. These features are in active development and prioritised based on design partner feedback.
We're onboarding a small group of design partners — data teams and compliance specialists who want governance tooling that fits how they actually work, not how enterprise vendors think they work.